In the almost mystical way that the Internet captures our innermost desires in the form of targeted advertisements, I came across Simon Singh’s The Code Book during a period of serious contemplation about whether to switch course from studying entanglements of DNA to becoming a Bond-esque secret agent. Once I was distanced from my naivete by a few chapters, however, I realized there is more to the history and science of cryptography than decrypting wartime messages and hacking into emails.
As I attempt to describe this deep dive into code breaking, I realize that the word ‘evolution’ is key. Singh effectively crafts a narrative that turns cyphers into living, breathing beings that mutate from their humble beginnings as ancient hieroglyphics, into complex mathematical equations, that ultimately land on the shore of Internet surfing — communication by email. The incessant tug-of-war between code-makers and code-breakers kept my eyes darting from page to page as every seemingly unbreakable, gradually more complex code was peeled back to its essence and disposed of resourcefully.
A huge contributor to the charm of The Code Book is its interdisciplinary approach, bringing together interesting and relevant stories from the annals of history, archaeology, computer science, mathematics, and linguistics. It highlights problems and solutions that at first glance do not seem to have anything to do with cryptography, but the author then goes on to make a strong case for its inclusion that broadens a reader’s perspective on just what exactly a “code” could be.
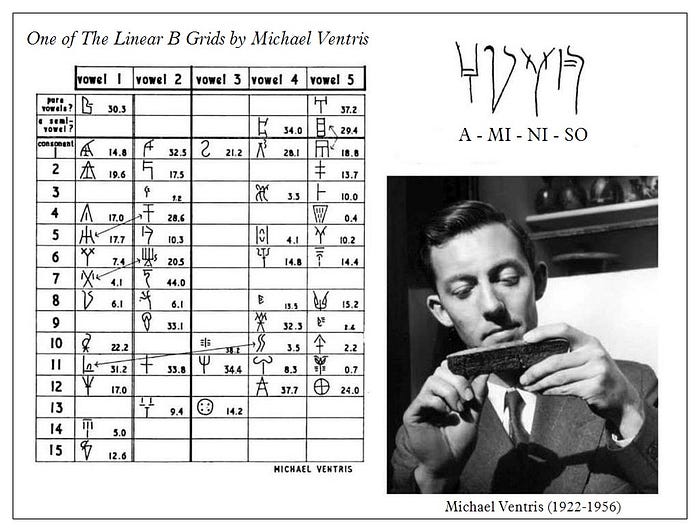
One such example is the unravelling of the Linear B Mycenaean Greek script, hitherto unreadable, using basic cryptographic techniques. By connecting certain frequently occurring words with known proper nouns, and performing frequency analysis (used to analyse the number of times a particular symbol occurs in the writing sample and assign frequently used letters to it), a “dead” language was revived – a strong case for the usefulness of code-breaking knowledge beyond the world of technology.
In another anecdote, Singh recalls the recruitment of Native American Navajo speakers by the United States army to act as code talkers and transmit undecipherable messages during WWII. The beauty of the Navajo language lies in its unique grammar, which even differentiates it from the other languages that belong to the same Na-Dene family. Unfamiliar words denoting battle equipment were given alternative names, like ‘shark’ in place of ‘destroyer’. Since it was an unwritten language at the time, only the Navajo speakers trained by the military had any hope of deciphering the messages. This code was so successful that it was even used in the Korean War, and has the distinction of being the only code used in the military that has not been deciphered.

Other historical references include the fairly central Enigma machine in all its mechanical glory, and the arduous efforts of Bletchley Park to crack the code. Secrecy and betrayal are abundant throughout the narrative, especially with regards to the British government who apparently distributed these machines throughout their former colonies without revealing that the cipher was no longer secure, in order to gain access to their communications.
/https://public-media.si-cdn.com/filer/f5/95/f59548db-c8c7-47a0-8404-9e44cd4b8db6/enigma.jpg)
Singh also speculates that perhaps Charles Babbage kept his cracking of the Vigenère cipher secret due to pressure from British Intelligence, leading to loss of recognition for his achievements until almost a hundred years afterwards. In fact, the secret nature of cryptographic research has its fair share of heartbreaking stories, where brilliant code-breakers have had to keep mum on their world-changing discoveries in order to safeguard the security of their country, and many of these discoveries have only been revealed after their deaths. Of course, this begs the question — what breakthroughs are being made in top-secret laboratories right now, and when will we ever learn of them?
By intercepting the text with cyphers that the readers are encouraged to crack on their own, Singh also keeps our attention and reinforces the principles we have learned by ensuring constant mental application. The step-by-step examples too are well-charted out and interesting enough that drifting or skipping through them is not really an option. We are also encouraged to create our own cyphers and codes, which may be easier to uncover than a standard encryption system, but are infinitely more fun.
This book is a great place to begin with learning about cryptography, and the extensive bibliography is a great resource for diving in a bit deeper. The detailed math in certain sections may be a bit of a turn-off for less mathematically inclined readers, and certain details, such as the descriptions of the Turing machine did seem over-the-top and difficult to understand, even though it was accompanied by pictures.
Ultimately, this book is great for that rare combination of history-and-mathematics nerds – people who can appreciate the irony of Mary, Queen of Scots’ own code being used against her, and marvel at the sheer brilliance of using Native American languages to communicate in wars. It will turn you into a fun facts-spouting machine for a few months, and you will see patterns all around you for a lifetime.
Leave a Reply